Welcome to a world of limitless possibilities in the Information Technology realm. We specialize in Cybersecurity and utilize the NIST framework to keep you and your customers’ data secure. Whether it’s data in motion or data at rest, we will make sure your information security is effortless while ensuring compliance and regulatory adherence.
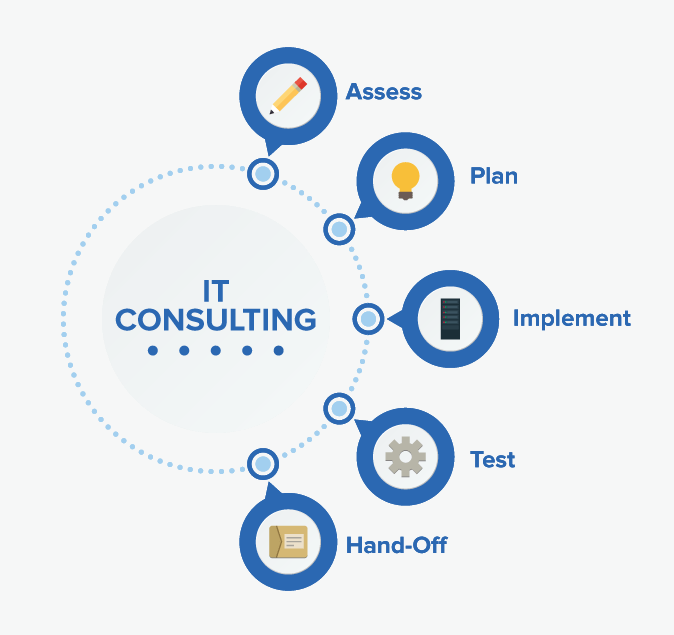
IT Consulting
IT Infrastructure Services
- Network design, implementation, and optimization
- Server setup, configuration, and management
- Storage solutions architecture and deployment
- Virtualization and cloud computing services
Data Management and Backup
- Data backup and disaster recovery planning
- Data storage solutions (on-premises and cloud-based)
- Data encryption and protection strategies
- Database administration and optimization
Business Continuity and IT Strategy
- Business continuity planning
- IT strategy development and implementation
- Technology roadmap planning
- IT governance and compliance consulting
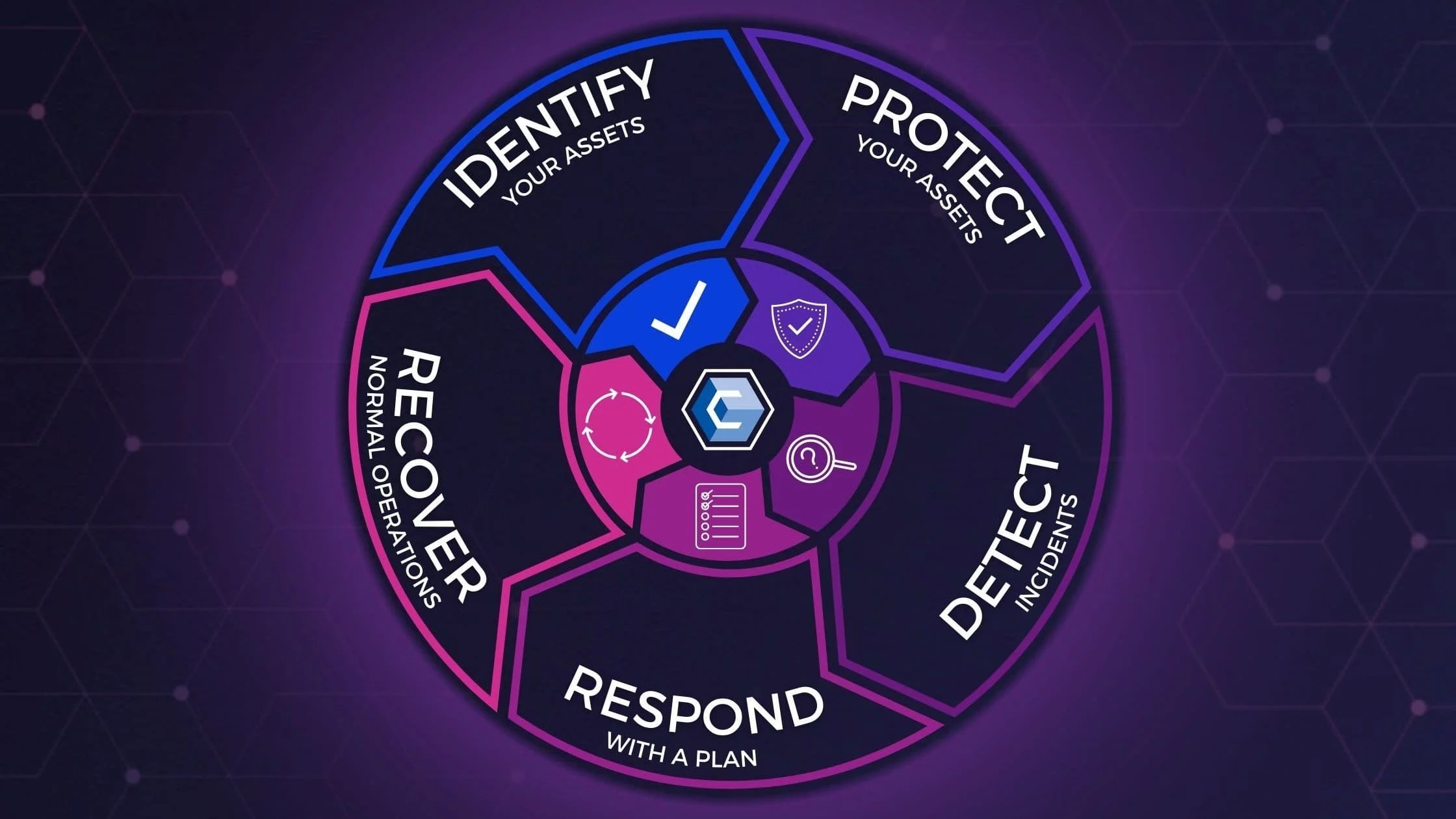
Cybersecurity Consulting
Cyber Risk Assessment and Management
- Threat intelligence analysis
- Vulnerability assessments
- Risk profiling and prioritization
- Regulatory compliance assessments (e.g., GDPR, HIPAA, etc.)
Incident Response and Forensics
- Incident response planning
- Cyber incident investigations
- Digital forensics analysis
- Incident recovery and remediation
Security Testing and Assessment
- Penetration testing (pen testing)
- Vulnerability scanning and assessment
- Security code reviews
- Red team/blue team exercises
Security Awareness Training
- Employee cybersecurity training programs
- Phishing simulation exercises
- Security policy development and implementation
- Security awareness workshops and seminars

Compliance and Regulatory Consulting
Compliance and Regulatory
- Compliance assessments (e.g., PCI DSS, ISO 27001, etc.)
- Regulatory compliance consulting
- Data privacy and protection advisory services
- Security audit and gap analysis
Security Governance and Strategy
- Security policy development and review
- Security risk management frameworks
- Security program maturity assessments
- Board-level cybersecurity advisory services
